This article mainly introduces the common methods of cracking the internal password of the single-chip microcomputer, explaining the methods and steps of cracking the single-chip microcomputer in detail, and briefly expounding some views on the cracking of the single-chip microcomputer.
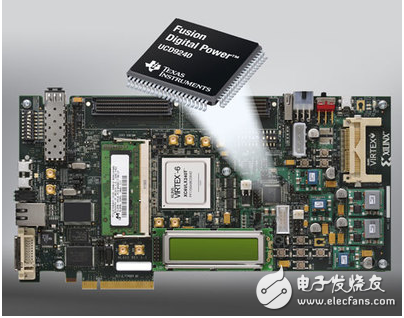
Chip decryptionChip decryption is also called MCU decryption, MCU cracking, chip cracking, and IC decryption. We are accustomed to calling CPLD decryption and DSP decryption as chip decryption. With the help of special or self-made equipment, the attacker of the single-chip microcomputer uses the loopholes or software defects in the design of the single-chip microcomputer to extract key information through various technical means, and obtain the program in the single-chip microcomputer is the chip decryption technology.
Chip decryption is an industry on the edge of the law, but the benevolent sees the benevolent and the wise sees the wisdom. A person in charge said that the chip decryption is just a knife, and there is no right or wrong in itself. It is just who holds it in the hand and what to do with the knife that ultimately determines its nature.
Regardless of the nature of chip decryption, the chip decryption technology itself is also a sophisticated high-end technology that requires crackers to have solid reverse engineering knowledge and rich decryption experience. Otherwise, it is very likely that the decryption will fail, losing the "master film" and losing troops.
How to decrypt the MCUMicrocontrollers (Microcontroller) generally have internal ROM/EEPROM/FLASH for users to store programs. In order to prevent unauthorized access or copying of the internal program of the single-chip microcomputer, most of the single-chip microcomputers have an encrypted lock bit or encrypted byte to protect the on-chip program. If the encryption lock bit is enabled (locked) during programming, the program in the single-chip microcomputer cannot be directly read with an ordinary programmer. This is the so-called copy protection or lock function. In fact, such protection measures are very fragile and can be easily cracked. With the help of special equipment or self-made equipment, a single-chip microcomputer attacker can use a variety of technical methods to extract key information from the chip and obtain programs in the single-chip microcomputer. Therefore, as a design engineer of electronic products, it is very necessary to understand the latest technology of current MCU attacks, to know oneself and the enemy, and to have a good idea, in order to effectively prevent the products that they have spent a lot of money and time working hard to design from being counterfeited overnight. occur.
SCM Decryption Technology EncyclopediaMCU Attack Technology
Currently, there are four main techniques for attacking MCUs, namely:
(1) Software attacks
This technology usually uses the processor communication interface and uses protocols, encryption algorithms, or security vulnerabilities in these algorithms to attack. A typical example of a successful software attack is the attack on the early ATMEL AT89C series single-chip computers. The attacker took advantage of the loopholes in the design of the erasing operation timing of this series of single-chip microcomputers. After erasing the encryption lock bit, the attacker stopped the next step of erasing the on-chip program memory data by using a self-programmed program, so that the encrypted single-chip microcomputer became Unencrypted single-chip microcomputer, and then use the programmer to read the on-chip program. At present, on the basis of other encryption methods, some equipment can be researched and cooperated with certain software to perform software attacks. Recently, a 51 single-chip decryption device (developed by a master in Chengdu) has appeared in China. This decryptor is mainly aimed at SyncMos. Winbond. The loopholes in the production process use some programmers to locate the insert bytes and pass certain The method finds whether there are continuous vacancies in the chip, that is, to find the continuous FF FF bytes in the chip, the inserted bytes can execute the instruction to send the program on the chip to the outside, and then use the decryption device to intercept it. The program inside the chip is decrypted and completed.
(2) Electronic detection attack
This technology usually monitors the analog characteristics of all power and interface connections of the processor during normal operation with high time resolution, and implements attacks by monitoring its electromagnetic radiation characteristics. Because the microcontroller is an active electronic device, when it executes different commands, the corresponding power consumption changes accordingly. In this way, by using special electronic measuring instruments and mathematical statistical methods to analyze and detect these changes, specific key information in the microcontroller can be obtained. At present, the RF programmer can directly read the program in the encrypted MCU of the old model, which is based on this principle.
(3) Fault generation technology
This technique uses abnormal operating conditions to cause processor errors, and then provides additional access to attack. The most widely used methods of fault generation attack include voltage shock and clock shock. Low-voltage and high-voltage attacks can be used to disable protection circuits or force the processor to perform incorrect operations. A clock transient may reset the protection circuit without destroying the protected information. Power and clock transients can affect the decoding and execution of a single instruction in some processors.
(4) Probe technology
This technology directly exposes the internal wiring of the chip, and then observes, controls, and interferes with the microcontroller to achieve the purpose of attack.
For the sake of convenience, people divide the above four attack techniques into two categories. One is intrusive attacks (physical attacks). This type of attack needs to destroy the package, and then use semiconductor test equipment, microscopes and micro-positioners in a dedicated laboratory. It takes hours or even weeks to complete. All microprobe technologies are invasive attacks. The other three methods are non-intrusive attacks, and the attacked MCU will not be physically damaged. Non-intrusive attacks are particularly dangerous in some situations, because the equipment required for non-intrusive attacks can usually be self-made and upgraded, so it is very cheap. Most non-intrusive attacks require the attacker to have good processor knowledge and software knowledge. In contrast, invasive probe attacks do not require much initial knowledge, and a complete set of similar techniques can usually be used against a wide range of products. Therefore, attacks on single-chip computers often start with invasive reverse engineering, and the accumulated experience helps to develop cheaper and faster non-invasive attack techniques.
The general process of an invasive attack
The first step of an intrusive attack is to remove the chip package ("opening" for short, sometimes called "opening", and "DECAP" in English, decapsulation). There are two ways to achieve this goal: The first is to completely dissolve the chip package and expose the metal connections. The second is to remove only the plastic package on the silicon core. The first method needs to bind the chip to the test fixture and operate it with the help of a binding table. The second method requires not only the knowledge and necessary skills of the attacker, but also the wisdom and patience of the individual, but it is relatively convenient to operate and is completely operated at home.
The plastic on the chip can be removed with a knife, and the epoxy resin around the chip can be etched away with concentrated nitric acid. Hot concentrated nitric acid will dissolve the chip package without affecting the chip and connections. This process is generally carried out under very dry conditions, because the presence of water may erode the exposed aluminum wire connections (which may cause decryption failure). The last step is to find the location of the protection fuse and expose the protection fuse to ultraviolet light. Generally, a microscope with a magnification of at least 100 times is used to trace in the wiring of the programming voltage input pin to find the protection fuse. If there is no microscope, a simple search is performed by exposing different parts of the chip to ultraviolet light and observing the results. During operation, opaque paper should be used to cover the chip to protect the program memory from being erased by ultraviolet light. Exposing the protective fuse to ultraviolet light for 5-10 minutes can destroy the protective effect of the protective bit. After that, the content of the program memory can be read directly using a simple programmer.
For the single-chip microcomputer that uses the protective layer to protect the EEPROM unit, it is not feasible to use the ultraviolet light to reset the protection circuit. For this type of microcontroller, micro-probe technology is generally used to read the memory content. After the chip package is opened, the data bus from the memory to the rest of the circuit can be easily found by placing the chip under the microscope. For some reason, the chip lock bit does not lock access to the memory in programming mode. Use this defect to put the probe on the data line to read all the desired data. In programming mode, restart the reading process and connect the probe to another data line to read all the information in the program and data memory.
The first step of an intrusive attack is to remove the chip package ("opening" for short, sometimes called "opening", and "DECAP" in English, decapsulation). There are two ways to achieve this goal: The first is to completely dissolve the chip package and expose the metal connections. The second is to remove only the plastic package on the silicon core. The first method needs to bind the chip to the test fixture and operate it with the help of a binding table. The second method requires not only the knowledge and necessary skills of the attacker, but also personal wisdom and patience, but it is relatively convenient to operate.
The plastic on the chip can be removed with a knife, and the epoxy resin around the chip can be etched away with concentrated nitric acid. Hot concentrated nitric acid will dissolve the chip package without affecting the chip and connections. This process is generally carried out under very dry conditions, because the presence of water may erode the exposed aluminum wire connections (which may cause decryption failure).
Next, the chip was cleaned with acetone in an ultrasonic bath to remove residual nitric acid, and then cleaned with water to remove salt and dried. Without an ultrasound bath, this step is generally skipped. In this case, the surface of the chip will be a little dirty, but it does not affect the operation effect of the ultraviolet light on the chip.
The last step is to find the location of the protection fuse and expose the protection fuse to ultraviolet light. Generally, a microscope with a magnification of at least 100 times is used to trace in the wiring of the programming voltage input pin to find the protection fuse. If there is no microscope, a simple search is performed by exposing different parts of the chip to ultraviolet light and observing the results. During operation, opaque paper should be used to cover the chip to protect the program memory from being erased by ultraviolet light. Exposing the protective fuse to ultraviolet light for 5-10 minutes can destroy the protective effect of the protective bit. After that, the content of the program memory can be read directly using a simple programmer.
For the single-chip microcomputer that uses the protective layer to protect the EEPROM unit, it is not feasible to use the ultraviolet light to reset the protection circuit. For this type of microcontroller, micro-probe technology is generally used to read the memory content. After the chip package is opened, the data bus from the memory to the rest of the circuit can be easily found by placing the chip under the microscope. For some reason, the chip lock bit does not lock access to the memory in programming mode. Use this defect to put the probe on the data line to read all the desired data. In programming mode, restart the reading process and connect the probe to another data line to read all the information in the program and data memory.
Another possible attack method is to use equipment such as microscopes and laser cutting machines to find protective fuses, so as to search for all signal lines connected to this part of the circuit. Due to the design flaws, as long as one of the signal wires from the protection fuse to other circuits is cut (or the entire encryption circuit is cut) or 1 to 3 gold wires (usually called FIB: focused ion beam) are connected, it can be Disable the entire protection function, so that the contents of the program memory can be read directly using a simple programmer. Although most ordinary single-chip microcomputers have the function of fuse blowing to protect the code in the single-chip microcomputer, since the general low-end single-chip microcomputers are not positioned to make safety products, they often do not provide targeted preventive measures and have low security levels. In addition, the application of single-chip microcomputers is wide, the sales volume is large, the entrusted processing and technology transfer between manufacturers are frequent, and a large amount of technical information is leaked out. This makes the use of the design loopholes of this type of chip and the test interface of the manufacturer, and the modification of the fuse protection bit and other invasive types It is easier to read the internal program of the microcontroller by means of attack or non-intrusive attack.
The general method of MCU decryptionMCU encryption and decryption can be divided into two categories, one is hardware encryption and decryption, and the other is software encryption and decryption. Hardware encryption. For single-chip microcomputers, it is generally the single-chip manufacturer that solidifies the encrypted fuse in the IC. The fuse has an encrypted state and an unencrypted state. If it is in an encrypted state, the general tools cannot read the program content in the IC. To read its content, which involves hardware decryption, you must have professional hardware decryption tools and professional engineers.
In fact, in theory, an attacker can use the above methods to break through with sufficient investment and time. This is a basic principle that system designers should always keep in mind. Therefore, as a design engineer of electronic products, it is very necessary to understand the latest technology of current MCU attacks, know yourself and the enemy, and have a good idea, in order to effectively prevent yourself from spending a lot of money and time. It happened that the designed product was counterfeited overnight.
Although most ordinary single-chip microcomputers have the function of fuse blowing to protect the code in the single-chip microcomputer, since the general low-end single-chip microcomputers are not positioned to make safety products, they often do not provide targeted preventive measures and have low security levels. In addition, the application of single-chip microcomputers is wide, the sales volume is large, the entrusted processing and technology transfer between manufacturers are frequent, and a large amount of technical information is leaked out. This makes the use of the design loopholes of this type of chip and the test interface of the manufacturer, and the modification of the fuse protection bit and other invasive types It is easier to read the internal program of the microcontroller by means of attack or non-intrusive attack.
to sum upAs we all know, at present, all the fields related to the decryption of single-chip microcomputers are generally used for product copying. It can not be said that there is no real use for research and learning, but it is quite rare. Therefore, if you want to crack the SCM decryption chip, you must know the principle of the SCM decryption chip. Therefore, for those who want to crack the microcontroller, study hard is the right way.
Lead-acid-lithium Hybrid Power System
High Rate Performance Power System,Backup Power System,Lead-Acid-Lithium System Integration,Lead-Acid-Lithium Hybrid Power System
Wolong Electric Group Zhejiang Dengta Power Source Co.,Ltd , https://www.wldtbattery.com